Google Authenticator is a popular two-factor authentication application that provides an extra layer of security to online accounts by generating time-based one-time passwords (TOTP). This technology makes it harder for hackers to access accounts even if they have the login credentials, as they would also need access to the user's phone to generate the TOTP.
While Google Authenticator is most commonly used on mobile devices, there are ways to use it on a PC as well. In this article, we'll explore how to set up Google Authenticator on your PC and how to use it to secure your online accounts.
Exporting 2FA from Google to your PC
To do this, you will need the "secret code" for Google Authenticator. This is the seed from which code generators can create code that works with Google.
To get the secret code, go to the Google Account Security Page . Go to the "Sign in to Google" section and click on "Two-Step Verification".
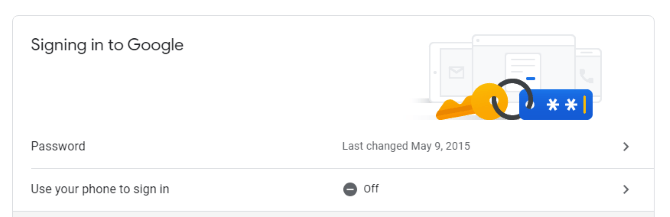
If Google knows that you have a phone connected to your account, it will walk you through the steps to set up a basic phone notification service.
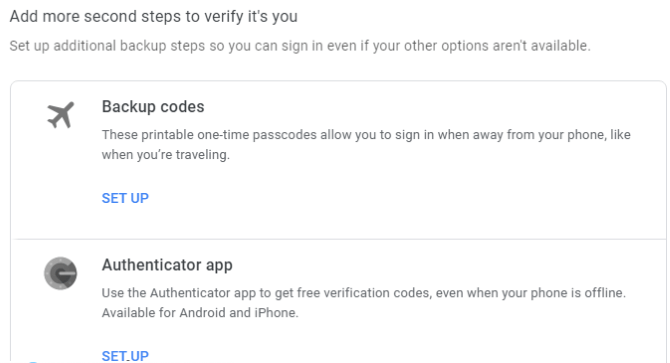
After you have completed the steps, you will have the opportunity to configure the Authenticator app. While we are not going to download the actual application, we must pretend that we are obtaining the secret key. Click on "Configure".
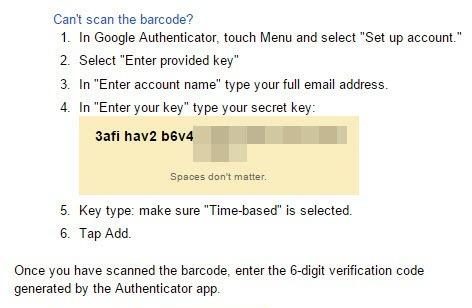
Follow the prompts until it asks you to scan a QR code. Below the code, click "Can't scan it?"
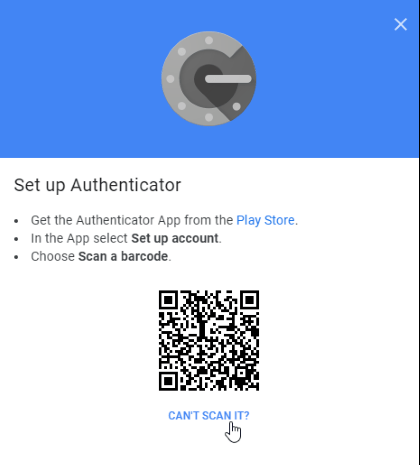
On the next page, find the secret key and copy it. This is what you will enter into third-party applications when they request a key. However, be sure to keep it a secret. If someone else gets this information, they can use it to log into your account!
Now that we have the code, let's see where we can put it.
1. Setting up Google Authenticator on PC using WinAuth
If you're concerned about a third-party app stealing or leaking your code, try WinAuth . Its main attraction is that it is an open source application that you can download to your PC. As such, there is no obfuscated code or cloud storage that can leak your key.
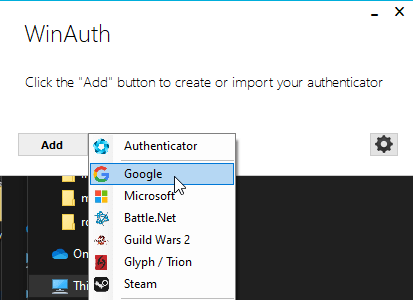
Configuration with WinAuth is very easy. Once WinAuth is running, add a new Google account.
Enter your private key, then click the "Verify authenticator" button. Continue with your Google account setup and enter the code that WinAuth provides.
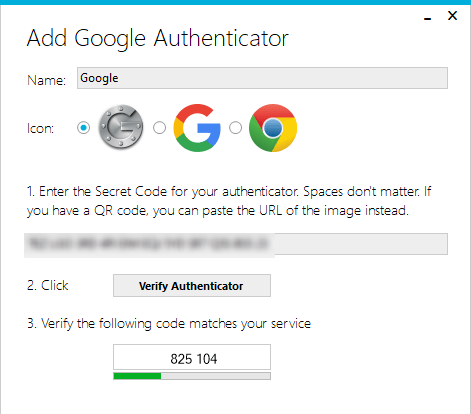
Copy the generated one-time password and paste it into your Google security settings page and click the "Verify and save" button to verify the generated code.
If everything is done correctly, Google will show you a confirmation window informing you. Just click the "OK" button to save the changes to your Google account.
Return to the WinAuth window: Now that you have committed the generated code, click the OK button to save the changes to the WinAuth application.
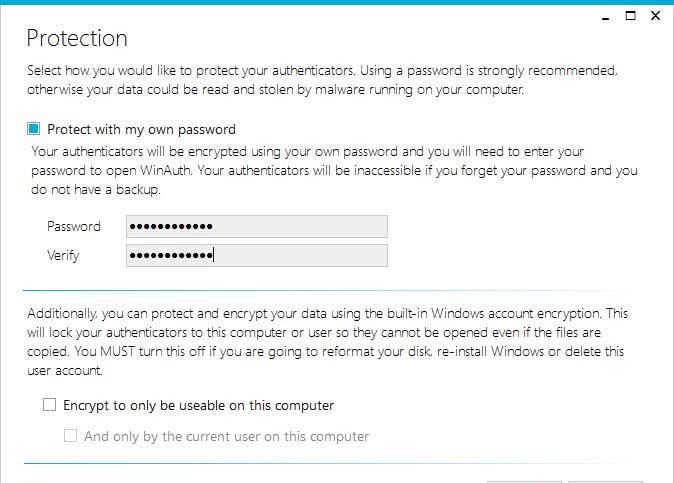
As soon as you click the "OK" button, WinAuth will open the Protection window that allows you to set a password to encrypt files saved by WinAuth. This ensures that any unauthorized access will be blocked. Simply enter the password twice and click the "OK" button to save the changes. Alternatively, you can also configure WinAuth to encrypt files so that it can only be used on the current computer, but using password protection is much more viable.
Now you can use Google Authenticator on your PC using WinAuth.
2. Setting up Google Authenticator on PC using Authy
If you want to sync your mobile and PC codes, try Authy. You can use it independently on your PC, but it asks for your phone details during registration. If you have Authy on your phone, you can quickly sync your data between the two devices.
In the PC version of Authy, click the plus icon in the upper right.
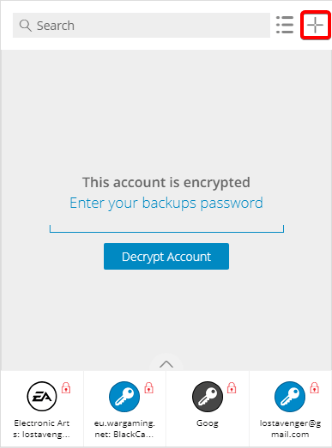
Paste the secret key in the box.
You can name and color the account. Once you've set it up, you'll have a working Google code.
3. Setting up Google Authenticator on PC using GAuth authenticator
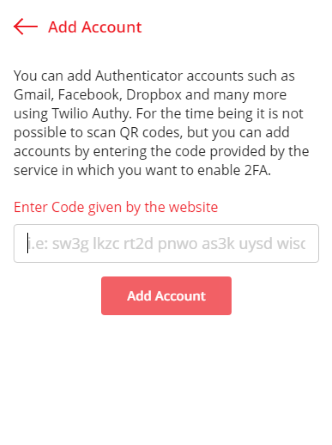
If you want something in your browser, you can try GAuth Authenticator. You can install it as a Chrome Extension or a Web App .
Adding your authenticator to GAuth is easy. First, click on the pencil in the upper right, then click Add.
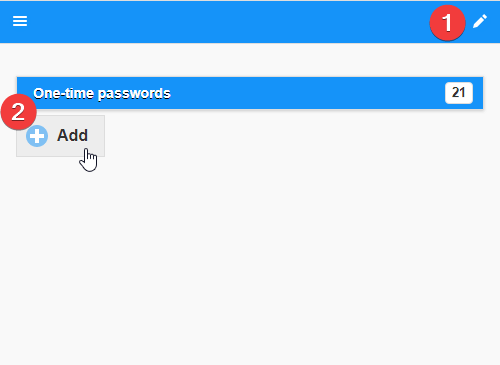
Enter the name of the authentication code (in this case, Google) and the secret key.
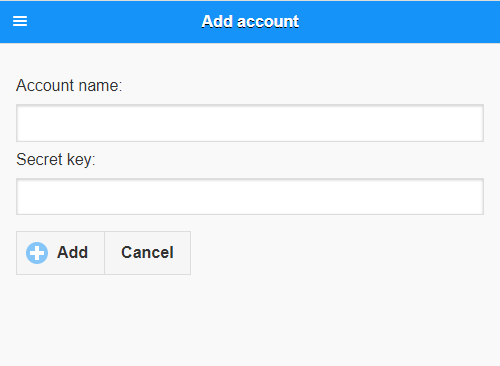
Once this is done, you will have a working authenticator.
4. Setting up Google Authenticator on PC using BlueStacks:
To use Google Authenticator on your PC, you will need an Android emulator. This is software that enables you to run Android applications on your PC. Some popular Android emulators include BlueStacks, NoxPlayer, and LDPlayer.
Here's how to set up Google Authenticator on your PC using BlueStacks:
Step 1: Download and install BlueStacks on your PC.
Step 2: Open BlueStacks and sign in to your Google account.
Step 3: Open the Google Play Store within BlueStacks and search for "Google Authenticator."
Step 4: Download and install the Google Authenticator app.
Step 5: Open the Google Authenticator app within BlueStacks and scan the QR code provided by the online service you want to secure. This will add the account to Google Authenticator and generate a unique TOTP.
Using Google Authenticator on PC:
Once you've set up Google Authenticator on your PC, you can use it just as you would on a mobile device. When you log in to a service that requires two-factor authentication, you'll be prompted to enter the six-digit code generated by Google Authenticator. Simply open the app within BlueStacks, and the code will be displayed.
Keep in mind that while Google Authenticator provides an extra layer of security to your online accounts, it's not foolproof. If your phone is lost or stolen, you won't be able to generate TOTPs unless you've backed up your Google Authenticator codes or set up alternative two-factor authentication methods. Additionally, if your PC is compromised, an attacker may be able to access your Google Authenticator codes and use them to access your online accounts.
Conclusion:
Google Authenticator is a simple yet effective way to secure your online accounts with two-factor authentication. While it's most commonly used on mobile devices, you can also use it on your PC with an Android emulator. By following the steps outlined in this article, you can set up and use Google Authenticator on your PC to protect your online accounts from unauthorized access. However, remember to keep your phone and PC secure to ensure the effectiveness of the two-factor authentication method.
The above tutorial published at Collaborative Research Group is for informational and educational purposes only and has been developed by referring to reliable sources and recommendations from technology experts. We do not have any contact with official entities nor do we intend to replace the information that they emit.
Passionate about understanding and contributing to a world that does not stop changing. New forms of Work, Sustainability and Technology. For many years he has worked as a creative for large international companies. He has a Ph.D. in information technology and he has been doing quantitative research in the interdisciplinary areas of information systems, cyber security, data analytics and artificial intelligence. He continue to look for creative solutions through technology to help companies to be more humane and sustainable..
Leave a reply
Your email address will not be published. Required fields are marked *Recent post

Examples of Using Wget Command for Windows and Linux
Laravel Tutorial for Beginners Step By Step (Manual Installation)

Withdraw Funds From PayPal to SberBank Card

How to install WhatsApp on the Nokia 3310